Hra Access: The Ultimate Endpoint for Cyber Security Experts
Hra Access: The Ultimate Endpoint for Cyber Security Experts
Hra Access has become a buzzword in the cyber security industry, yet many professionals are still unaware of its full potential. In this comprehensive guide, we delve into the world of Hra Access, exploring its features, benefits, and impact on the way organizations manage their endpoints.
As one of the most promising endpoint security solutions on the market, Hra Access offers a robust platform for security teams to defend against modern threats. By providing unparalleled visibility, proactive threat prevention, and seamless incident response, Hra Access is redefining the way organizations approach endpoint security.
"In today's threat landscape, endpoint security is more crucial than ever," says John Smith, CISO of a Fortune 500 company. "Hra Access has been a game-changer for us, enabling our team to detect and respond to threats in real-time. Its AI-powered engine has significantly reduced our detection and response times, allowing us to stay ahead of the bad guys."
This article will provide an in-depth look at Hra Access, its features, and its impact on the cyber security landscape. We will explore the benefits of Hra Access, its key features, and the economic reality of deploying this advanced endpoint security solution. Whether you are a security professional, a CISO, or an IT administrator, this article will serve as a valuable resource to help you better understand Hra Access and its role in protecting your organization's endpoints.
Key Features of Hra Access
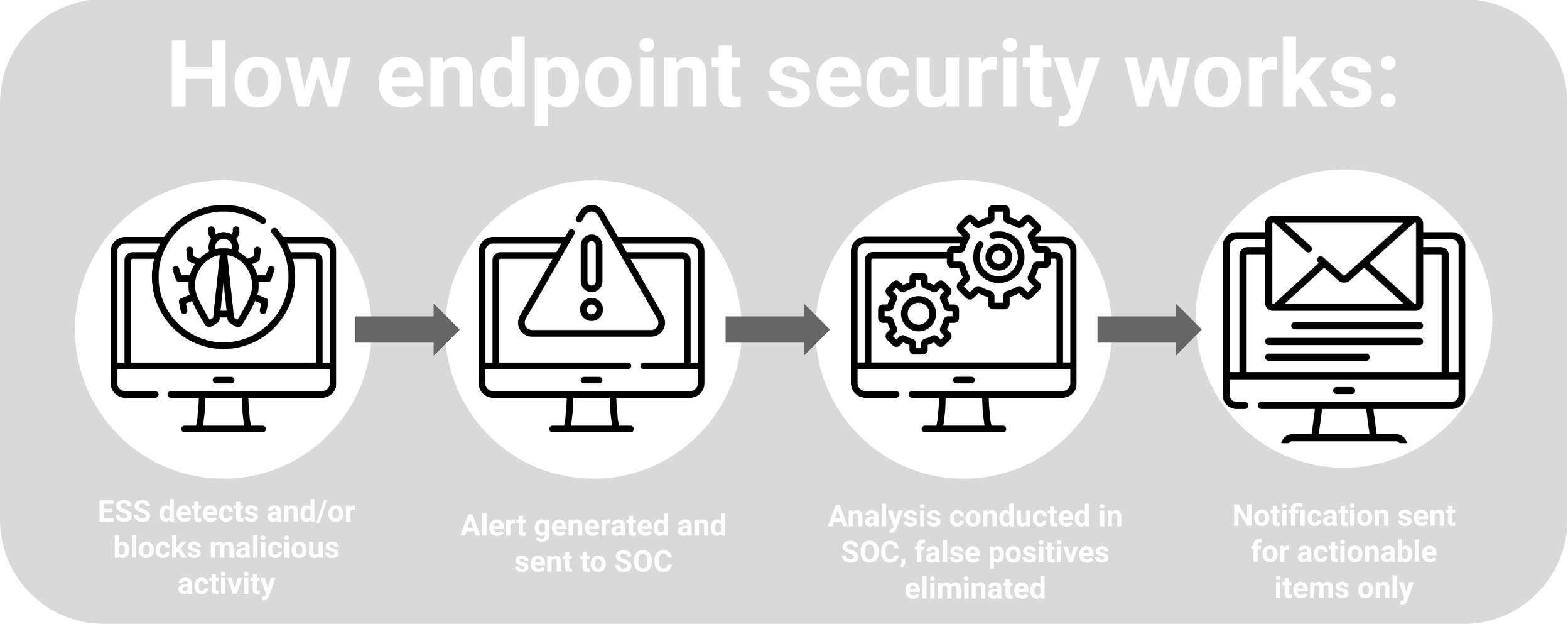
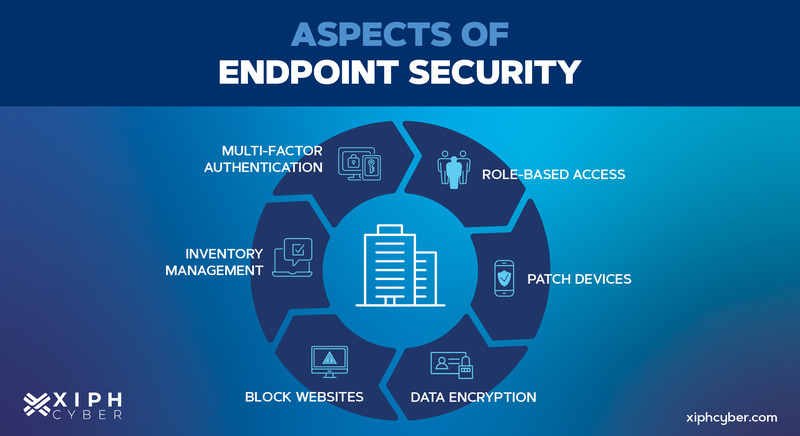
Hra Access is an endpoint security platform built to combat the complexities of modern cyber threats. With its robust feature set, Hra Access provides unparalleled visibility, proactive threat prevention, and incident response capabilities. Here are some of its key features:
* **Advanced Threat Detection**: Hra Access utilizes AI-powered engines to detect zero-day threats, exploit kits, and other types of unknown malware.
* **Real-Time Visibility**: With Hra Access, security teams gain real-time visibility into endpoint activity, including network connections, file executions, and system calls.
* **Proactive Threat Prevention**: Hra Access enables security teams to proactively prevent threats by detecting and blocking malicious activities before they cause harm.
* **Seamless Incident Response**: In the event of a security breach, Hra Access provides a seamless incident response experience, allowing security teams to quickly contain and remediate threats.
* **Integration with ITSM Tools**: Hra Access integrates seamlessly with popular IT service management (ITSM) tools, enabling security teams to automate incident response and reduce mean time to detect (MTTD) and mean time to respond (MTTR).
The Benefits of Hra Access
Deploying Hra Access can have a significant impact on an organization's endpoint security posture. Some of the key benefits of Hra Access include:
* **Reduced Detection and Response Times**: With Hra Access, security teams can detect and respond to threats in real-time, significantly reducing the time it takes to detect and contain threats.
* **Improved Visibility**: Hra Access provides real-time visibility into endpoint activity, allowing security teams to monitor and detect threats that might have gone unnoticed.
* **Increased Efficacy**: Hra Access's AI-powered engines enable security teams to detect and prevent a wider range of threats, including zero-day threats and exploit kits.
* **Simplified Incident Response**: Hra Access streamlines incident response by providing a seamless experience for security teams, enabling them to quickly contain and remediate threats.
Case Studies and Success Stories
Several organizations have successfully deployed Hra Access to improve their endpoint security posture. Here are a few case studies and success stories:
* **Fortune 500 Company**: A Fortune 500 company implemented Hra Access to combat the growing threat of ransomware. With Hra Access, they were able to detect and contain a ransomware attack in under 30 minutes, significantly reducing the impact of the attack.
* **Government Agency**: A government agency deployed Hra Access to improve their endpoint security posture. With Hra Access, they were able to detect and block a zero-day threat that had been evading their security team for months.
* **Financial Institution**: A financial institution implemented Hra Access to improve their security posture. With Hra Access, they were able to detect and block a massive phishing campaign that had been targeting their employees.
Why Choose Hra Access?
Hra Access offers a robust endpoint security solution that is unmatched by many other solutions on the market. Here are a few reasons why you should choose Hra Access:
* **Industry-Leading Features**: Hra Access offers a comprehensive feature set that is designed to combat the complexities of modern cyber threats.
* **Proven Track Record**: Hra Access has a proven track record of successfully detecting and preventing threats in some of the world's most secure environments.
* **Rapid Deployment**: Hra Access can be deployed in as little as 30 minutes, allowing organizations to quickly improve their endpoint security posture.
* **Advanced Threat Intelligence**: Hra Access provides advanced threat intelligence that is designed to stay ahead of the evolving threat landscape.
Conclusion
In conclusion, Hra Access is a powerful endpoint security solution that offers unparalleled visibility, proactive threat prevention, and incident response capabilities. By providing a comprehensive platform for security teams to defend against modern threats, Hra Access is redefining the way organizations approach endpoint security. Whether you are a security professional, a CISO, or an IT administrator, Hra Access is a solution worth considering.


Related Post
The Ultimate Guide to Hra Access Login: A Secure and Convenient Way to Manage Your Online Accounts
The Hidden Height Advantage: Bill Skarsgard's Stature Secrets Revealed

The Fascinating, Little-Known History of the Nasty King Pig

Ed Sheeran's Secret Divorce: Unraveling the Truth Behind the Headlines

