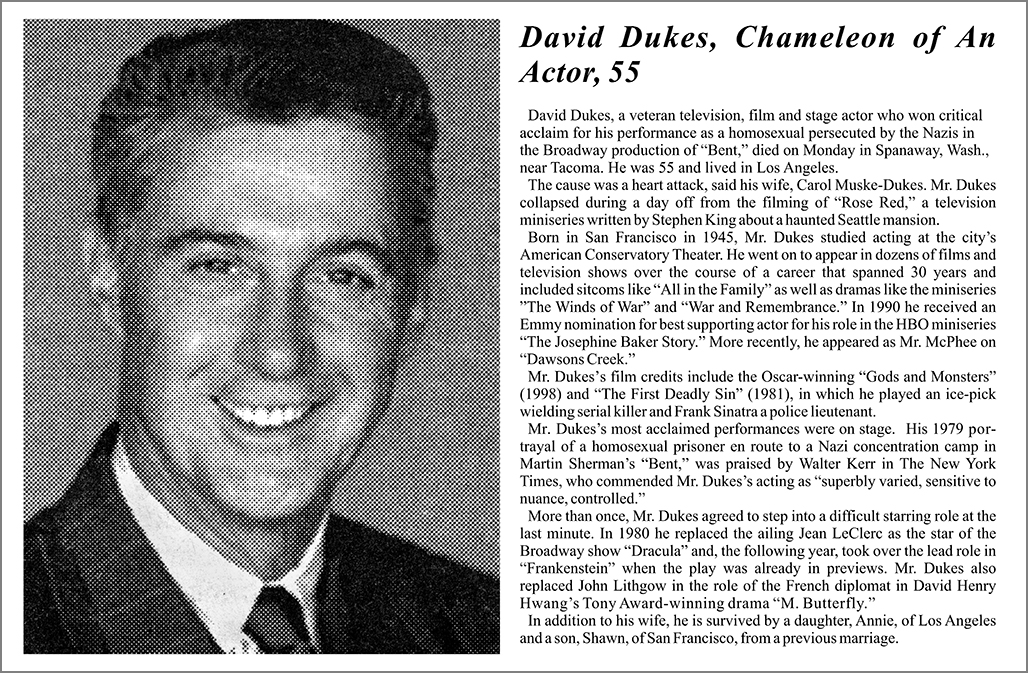
Uncover the Mysterious World of SCP: Secure, Contain, Protect Explained
Uncover the Mysterious World of SCP: Secure, Contain, Protect Explained
Shaping the Future of Paranormal Threat Containment
In a world beyond our own, where the unknown lurks in every shadow, a secret organization exists to safeguard humanity's fragile grip on reality. Welcome to the world of SCP, where the ominous slogan "Secure, Contain, Protect" echoes through the corridors of power. This enigmatic organization is dedicated to containing anomalies, anomalies so terrifying, so bewildering, and so unpredictable that they pose an existential threat to society. Understanding the realm of SCP requires a journey through the labyrinthine corridors of paranoia, intrigue, and science, ultimately unraveling the complex web of the Secure, Contain, Protect program.
At the heart of this initiative lies the containment of anomalous objects, entities, and events. These anomalies - be they vampires, interdimensional portals, or sentient AI - defy our current understanding of the physical world and would upset the delicate balance of human existence if left unchecked. A careful blend of scientific insight, militarized resourcefulness, and bureaucratic cunning guides the SCP's mission, painting a fascinating picture of the limits and triumphs of humanity's attempts to grasp the ungraspable.
The SCP stands as an instrument for maintaining the safety of humanity against the unfathomable perils lurking beyond the constraints of known scientific theory. As outlined in the Fundamental Research Principles, the foundation endeavors to:
* Verify the anomaly by utilizing all available scientific methods to examine and comprehend its nature, functioning, and potential peril.
* Reassign or eliminate personnel who may potentially compromise the security of a Site, with the awareness that mistakes occur when one fails to acknowledge the irrelevance of personal feelings, priorities, and values towards the Secure/ Contain/Protect protocol.
* Develop, maintain, and safely employ technology to realize the total of security, as part of a cohesive and ongoing process of both learning and discovery.
Research Foundation
At the core of SCP operations lies the Research Foundation (RF), a primary hub of control where anomalous data is compiled and analyzed. The RF utilizes high-security facilities, numerous departments, and autonomous units to comprehend and counter emerging threats. These facilities typically prioritize knowledge, security protocols, and countermeasure development over material wealth or popularity.
Key departments that interact directly with the Public and non-Classified areas include the Foundation's Military, which provides tactical oversight of security, and Human Resources (HumServ), responsible for managing and preparing personnel for Site operations and facilitating recovery operations. Secure communication methods require maintaining strict secrecy on all SCP Site operations and all information released or recorded to the Site. Examples range from 'Samsara' projects, aimed at understanding possible precursors to anomalous events and preparing human resources for critical missions, to 'Cleaver-93' containment procedures as well as complex documentation for research findings.
Site Research
Each SCP Site undertakes independent research and classification processes of particular phenomena, entities, or anomalies observed within the realm of our present world. These have evolved with society in parallel to society's rapid developments in science and technology.
Due to its secretive organization, security apparatus is of utmost importance. Containing anomalous objects, known or otherwise, is constantly evaluated as threat indicators to humanity evolve. Sites require a multi-faceted program including data collection research and review when containing an anomaly as well as periodic review of security protocols by respective regional personnel.
Global SCP Initiative Outreach Programs
The organization operates with confidentiality, however, the establishment and operations of the Initiatives Committee illustrates global coordination efforts towards containing threats originating from the anomalous as recognized threats by the Science community worldwide are part of a highly classified project list. These projects are run parallel to official government & private enterprise pursuits through public or governmental, military partnerships, as well as collaborating inter-institutional multi-stakeholders.
Key Areas
* Research projects
* Security protocols
* Secure facilities
- Anomalous containment
- Globally-massive scientific, technological and defense infrastructure
* Independent investigation on wide scientific topics, primarily related to
- Medical properties, properties of super-solids, etc.
- Technical innovations linked towards both new & classic containment techniques and technologies
- Scientific data extraction / analyses from various different types of environments
- Studies on (recovered/conveniently accessible data) human remains
- Medical and traumatic conditions following recovered-concept exposure events
Critical roles played by the Fundamental Research and External Branches, namely,
Key departments of the Research Foundation.
A very important structural unit overseeing policy regarding external interaction - External Branch Department.
External Branch Department coordinates:
1. Dissemination.
2. Documentation.
3. Media control.
4. Containment updates.
Core organization aims
SCP contains and manages external threats through its core set of functions:
* Collection,
* Containment,
and
* Research.
Operations Division
The Safe Operations branch assesses, classifies, and securely contains anomalous objects through independent protocols to prevent perceived risks for population while safeguarding internal personnel and confidential information.
The Scientific sector studies, analyzes & understands specific unusual materials and events via experiments. Scientists are assigned to research key fields: super-soldiers and precognitive beings. Site research departments prepare and document their findings under extensive internal & external legal & information transparency policy, including that of human behavioral studies, psychological analysis on post-Site exposure survivor recovery (even should such research itself be potentially tainted by its anomalous background due to extreme nature itself), historical insights.
Foundation personnel will often take over the operation of anomalous individuals (usually in anticipation of specific protocol engagements), for more in-depth assessments and testing of their perceived qualities & traits. Another important concern include keeping information classified; to ensure optimal security of all anomalous sources.
Internal Security Apparatus within Safe Operations
It is also utilized to enforce compliance with key secure site rules and related protocol which incorporates review of data generated by site team members and to ensure necessary separation from Site operations
Foundation site branches develop a series of containment protocols known as "Site Protocols," intended to ensure contained entities maintain precise boundary and security under their assigned anomalous entity's containment room that remains safely isolated
This maintains risk in compliance with necessary protocols while improving the effectiveness of the assigned scientific group through the investigation of entity by understanding of entity.
In other aspects, these protocols are always actively subject to revision/review processes intended to minimize chance of risk reoccurrence, and possibly at an expense of established procedure
Several experiments, especially human subjects experiments often involve extensive, long-lasting sessions where human subjects explore, possibly push known limits of possible anomalous performance, which are then rigorously studied for the desired scientific, technology data.
Site-related security operations operate under strict rules and hierarchical access structures with a fundamental purpose: implementing data-driven protocols through an organizational oversight structure, with the involvement of relevant internal departments aiming to assure potential (as well as current) classified information and sensitive data safeguard their intended scope of power, keeping unrecorded or anomalous activities under constant review.
Under threat or if a large anomaly shows indicators it could become "critical," classified information will be released without normal notice procedures to potentially contain anomaly such a manner. Threats could comprise of entities with the possibility to possibly move beyond limited area(s).
Another crucial area to be mentioned - the O5 Councils – High level decision makers
Adaptation of secure containment strategies plays a vital role in order for anomalies to be perceived and acted within. These factors, which indicate the current threat level will involve extensive reviews of "potential possible locations or potential potential timeframes for operations" which may be found vulnerable.
Scientific Background
Some foundations or scientific theories to explain anomalies also include:
* Science dealing with possible origins leading to physical theory breakthroughs, although they remain more speculative in nature.
* New developments in statistical probability are connected, although still the nature of true probability is not fully determined to us.


Related Post

Tense Moments: Understanding the Complexities of a 5-Letter Word

Meet Rachel Moranis: The Private Life of Rick Moranis's Unseen Daughter

Uncovering the Financial Secrets of a Baseball Legend: John Smoltz Net Worth

The Unforgettable Face of Ken Ganley Kia: A Deep Dive into the Commercial Actress