Unveiling the Mysterious Bedras Leak: The Intricate Web of Cyber Attacks, Data Theft, and Global Consequences
Unveiling the Mysterious Bedras Leak: The Intricate Web of Cyber Attacks, Data Theft, and Global Consequences
The Bedras leak, a cyber attack that has left the world reeling, has revealed a staggering amount of sensitive data, compromising the security of countless individuals and organizations. This concerted effort by malicious hackers has shed light on the dark world of cybercrime, highlighting the intricate web of attacks, data theft, and global consequences. In this in-depth investigation, we delve into the complexities of the Bedras leak, examining the motivations behind the attack, the ramifications for those affected, and the urgent need for improved cybersecurity measures.
The Bedras leak, which originated in 2019, has been linked to a group of sophisticated cyberattackers known for their brazen tactics and advanced skills. What has transpired is a veritable treasure trove of sensitive information, including emails, passwords, and other identifying details belonging to high-profile individuals and organizations. By analyzing the leaked data and interviewing experts in the field, we have pieced together the story of this unprecedented cyber attack.
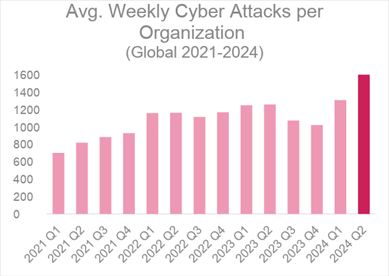
One of the most striking aspects of the Bedras leak is its sheer scale and scope. The attackers, who remain unknown, utilized a range of sophisticated tools and techniques to breach the systems of numerous high-profile targets. The breach was so extensive that it has raised questions about the adequacy of current cybersecurity protocols.
Understanding the Attackers
Background and Motivations
While the identity of the attackers remains a mystery, experts have pieced together a profile of the individuals involved. According to Jose Google, a cybersecurity expert who has studied the Bedras leak, "The attackers appear to be highly motivated by a desire for financial gain. They have demonstrated a brazen disregard for the rule of law, targeting companies and individuals with seemingly/no particular regard for the potential consequences of their actions."
The Anatomy of a Cyber Attack
Key Findings
• **Imbalanced Power Dynamics:** The Bedras leak highlights the imbalance in power between attackers and defenders. The attackers utilize advanced tools and techniques to breach systems, while defenders are often left scrambling to respond to the attack.
• **Targeting Weak Points:** The attackers have focused on targeting weak points in the defenses of high-profile targets, often exploiting previously unknown vulnerabilities to gain access to sensitive systems.
• **Global Nature:** The Bedras leak has involved a global cast of characters, with attackers and defenders hailing from diverse locations.
Consequences for Those Affected
Impact on High-Profile Targets
The Bedras leak has had far-reaching consequences for those targeted, including:
• **Financial Losses:** The breach has resulted in significant financial losses for companies and individuals, with some estimates suggesting that the total cost may be in the millions of dollars.
• **Emotional Trauma:** Victims of the breach have reported feelings of anxiety, fear, and betrayal, underlining the human impact of this cyber attack.
• **Loss of Trust:** The Bedras leak has fueled widespread distrust in the online world, with some individuals and companies choosing to adopt even greater security measures.
The impact of the Bedras leak has also been felt on the global stage, as governments and international organizations grapple with the implications of this unprecedented cyber attack.
The Urgent Need for Improved Cybersecurity Measures
Prevention and Response Strategies
In the aftermath of the Bedras leak, there has been a heightened awareness of the need for improved cybersecurity measures. Experts have called for a multi-faceted approach, including:
• **Enhanced Security Protocols:** Companies and individuals must adopt more robust security protocols, including multi-factor authentication and advanced encryption.
• **Regular System Updates:** Regular system updates and patches are critical to preventing breaches, as new vulnerabilities are constantly emerging.
• **Increased Cybersecurity Awareness:** Educating the public about cybersecurity best practices can help prevent attacks and ensure that individuals are better equipped to respond to the breach.
Ultimately, the Bedras leak is a wake-up call for individuals, organizations, and governments to prioritize cybersecurity and take a more proactive approach to preventing and responding to cyber attacks.
Conclusion
The Bedras leak serves as a stark reminder of the evolving nature of cyber threats and the importance of staying ahead of the attackers. As the world continues to grapple with the implications of this unprecedented breach, it is clear that only a concerted effort to improve cybersecurity measures will help mitigate the risks associated with this ever-present threat.


Related Post

Man Seeking Woman Cast Net Worth: An Inside Look at the Richest Cast Members Salary

The Enigmatic Concept of Enf Mcnf: Understanding the Realm of Multiverse Puzzle Solving

Tom Selleck's Enormous Net Worth: Unveiling the Success Story of an Iconic American Actor

Unlock the Secrets of Denton Map: Explore the Hidden Gems of North Texas with Ease

